Building a WireGuard VPN server on a Raspberry Pi is an efficient way to create a secure, private tunnel back to your home network from anywhere. This setup, often referred to as a wireguard home server, allows you to securely access local resources like network-attached storage (NAS) or security cameras, bypass geo-restrictions for personal content, and encrypt your traffic when using untrusted public Wi-Fi. Utilizing a wireguard raspberry pi combination offers excellent performance, especially on newer models, and complete control over your data, moving away from reliance on third-party VPN providers.
Hardware and OS Setup for Your WireGuard Raspberry Pi
To begin building your WireGuard home server, select a suitable Raspberry Pi model. Raspberry Pi 4 or 5 models are recommended due to their superior performance, capable of handling 300-400 Mbps throughput for WireGuard, which can saturate many home internet connections. Older models like the Pi Zero W are less suitable, offering limited throughput (10-20 Mbps) and higher CPU utilization.
For the operating system, download and flash Raspberry Pi OS Lite (64-bit) to a quality microSD card. A headless setup (no desktop environment) is preferred to conserve RAM and CPU resources. During the flashing process using Raspberry Pi Imager, enable SSH, set a username and strong password, and configure Wi-Fi for initial access if you plan to run it wirelessly.
Initial Raspberry Pi Configuration
Once the OS is installed and the Pi is booted, connect via SSH. Find your Pi's IP address on your router's client list or use network scanning tools. Then, connect:
ssh your_username@your_pi_ip_address
Immediately update your system to ensure all packages are current and secure:
sudo apt update && sudo apt upgrade -y
It is crucial to assign a static IP address to your Raspberry Pi on your local network. This prevents its IP from changing, which would break your VPN connection. Configure this through your router's DHCP reservation settings, linking the Pi's MAC address to a fixed IP outside your router's dynamic DHCP range.
Installing and Configuring WireGuard on Raspberry Pi
Installing WireGuard is straightforward. The WireGuard tools are available in the Raspberry Pi OS repositories. Execute the following commands:
sudo apt update
sudo apt install wireguard -y
Next, generate the necessary public and private keys for your WireGuard server. WireGuard uses cryptographic key pairs for secure communication between peers. Navigate to the WireGuard configuration directory and set strict permissions:
sudo -i
cd /etc/wireguard
umask 077
wg genkey | tee server_privatekey | wg pubkey > server_publickey
This generates two files: server_privatekey (which must remain secret) and server_publickey (which you will share with clients). Repeat this process for each client device, generating a unique pair for each. Keep track of which key belongs to which device.
Server and Client Configuration for Your WireGuard Home Server
Create the main server configuration file, typically named wg0.conf, in the /etc/wireguard/ directory. This file defines the server's interface and details for each client peer.
Server Configuration (/etc/wireguard/wg0.conf)
[Interface]
PrivateKey = <contents of server_privatekey>
Address = 10.0.0.1/24
ListenPort = 51820
PostUp = iptables -A FORWARD -i %i -j ACCEPT; iptables -A FORWARD -o %i -j ACCEPT; iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
PostDown = iptables -D FORWARD -i %i -j ACCEPT; iptables -D FORWARD -o %i -j ACCEPT; iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADE
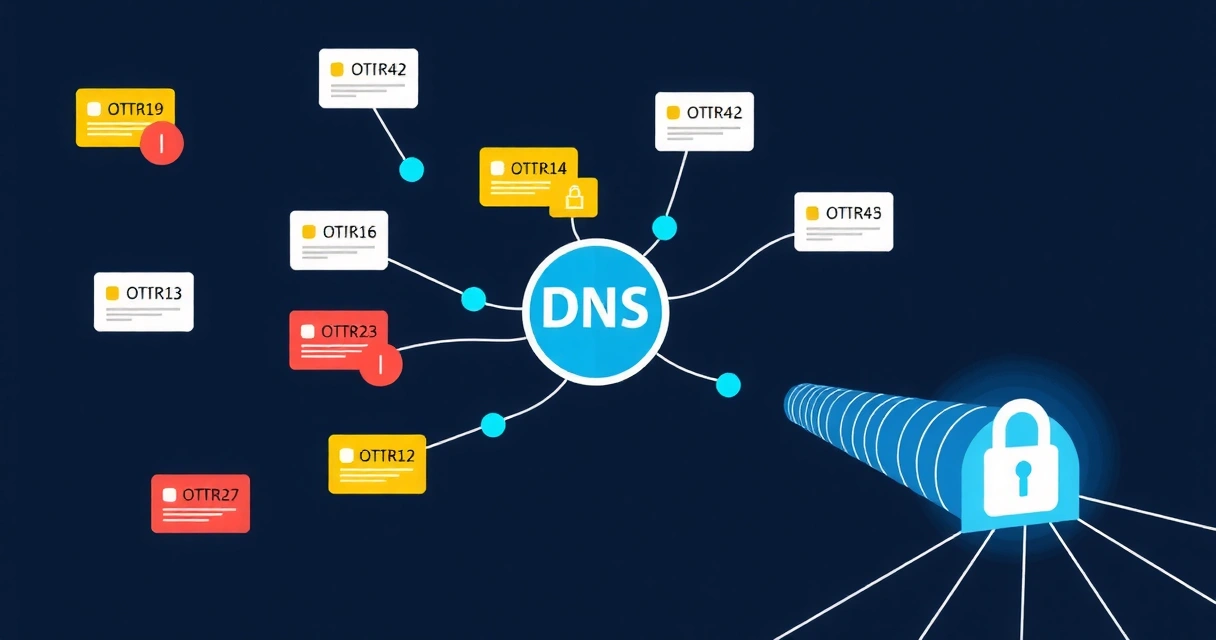
DNS = 192.168.1.1 # Your router's IP or a public DNS server like 1.1.1.1
# Client 1 (e.g., Your Phone)
[Peer]
PublicKey = <contents of client1_publickey>
AllowedIPs = 10.0.0.2/32
# Client 2 (e.g., Your Laptop)
[Peer]
PublicKey = <contents of client2_publickey>
AllowedIPs = 10.0.0.3/32
Explanation:
PrivateKey: The server's secret private key.Address: The IP address the WireGuard interface will use within the VPN tunnel.10.0.0.1/24creates a virtual network for your VPN clients.ListenPort: The UDP port WireGuard listens on for incoming connections (default is 51820).PostUp/PostDown: These commands manage NAT (Network Address Translation) and IP forwarding rules when the VPN interface comes up or goes down. Replaceeth0with your Pi's actual external network interface name (e.g.,wlan0if using Wi-Fi).DNS: Your desired DNS server for clients. This could be your home router, a Pi-hole on your network, or a public DNS service. Proper DNS configuration is vital to prevent DNS leaks.[Peer]: Each client is a peer.PublicKey: The public key generated for that specific client device.AllowedIPs: The IP address assigned to this client within the WireGuard tunnel. The/32mask ensures only this specific IP is routed for the client.
Client Configuration Example (client1.conf)
For each client, create a separate .conf file or use the WireGuard client app to generate a configuration. This example is for `client1`:
[Interface]
PrivateKey = <contents of client1_privatekey>
Address = 10.0.0.2/32
DNS = 10.0.0.1 # Your WireGuard server's tunnel IP
[Peer]
PublicKey = <contents of server_publickey>
Endpoint = your_home_public_ip_or_domain:51820
AllowedIPs = 0.0.0.0/0, ::/0
PersistentKeepalive = 25
Explanation:
PrivateKey: The client's unique private key.Address: The client's IP within the VPN tunnel, matching theAllowedIPson the server for this peer.DNS: Point this to your WireGuard server's tunnel IP (10.0.0.1) to use its DNS or any other desired DNS server.PublicKey: The public key of your WireGuard server.Endpoint: Your home network's public IP address or a Dynamic DNS hostname, followed by the WireGuard listening port. Services like Zondex can help you verify your public-facing network services.AllowedIPs = 0.0.0.0/0, ::/0: This directs all IPv4 and IPv6 traffic from the client through the VPN tunnel, creating a "full tunnel" VPN. If you only want to access your home network, you would specify your home LAN subnet here (e.g.,192.168.1.0/24).PersistentKeepalive = 25: Sends a packet every 25 seconds to keep the NAT connection open, useful for clients behind restrictive NAT or firewalls. This improves mobile VPN security.
Firewall Rules and Network Forwarding
For your WireGuard home server to function as a gateway for internet traffic and allow access to your home network, IP forwarding must be enabled, and firewall rules need to be configured.
Enable IP Forwarding
Edit /etc/sysctl.conf to enable IP forwarding. Uncomment or add the following line:
sudo nano /etc/sysctl.conf
net.ipv4.ip_forward=1
# For IPv6 if needed:
net.ipv6.conf.all.forwarding=1
Apply the changes:
sudo sysctl -p
Router Port Forwarding
You must configure your home router to forward the WireGuard UDP port (default 51820) from your router's public IP to your Raspberry Pi's static local IP address. The exact steps vary by router model, but typically involve:
- Logging into your router's administration panel.
- Navigating to "Port Forwarding" or "NAT" settings.
- Creating a new rule:
- External Port: 51820 (or your chosen port)
- Internal Port: 51820 (or your chosen port)
- Protocol: UDP
- Internal IP Address: Your Raspberry Pi's static IP (e.g., 192.168.1.100)
Always verify your router's external IP if you don't have a static public IP and consider setting up Dynamic DNS (DDNS) if your ISP assigns a dynamic IP address.
Starting and Enabling WireGuard
Start the WireGuard interface:
sudo wg-quick up wg0
Verify it's running:
sudo wg
To ensure WireGuard starts automatically on boot:
sudo systemctl enable wg-quick@wg0
Maintaining and Securing Your WireGuard Raspberry Pi VPN
Maintaining a secure WireGuard server requires ongoing attention. Regularly update your Raspberry Pi's operating system and WireGuard packages to patch any security vulnerabilities. Keep your keys secure and consider using a security assessment tool to scan your network for exposed services.
Security Best Practices:
- Strong Passwords & SSH Keys: Always use strong, unique passwords and consider disabling password-based SSH authentication in favor of SSH keys.
- Firewall Hardening: Beyond the basic NAT rules, configure a more comprehensive firewall (like UFW or nftables) to restrict access. Allow only necessary incoming connections (e.g., SSH, WireGuard UDP port). If using BiizTools for any other services on the Pi, ensure their ports are also explicitly allowed.
- No-Log Policy: While you control your own server, understanding the principles of a no-log VPN policy helps you ensure your server doesn't inadvertently log sensitive data.
- Physical Security: Secure your Raspberry Pi physically, as access to the device can compromise your VPN.
- Pre-Shared Keys (Optional): For an additional layer of security, you can generate and configure a pre-shared key (PSK) between each peer and the server. This provides post-quantum resistance.
# On server and client for a specific peer
wg genpsk > psk_client1
# Add to server's wg0.conf for Peer 1
[Peer]
...
PresharedKey = <contents of psk_client1>
# Add to client1.conf
[Interface]
...
[Peer]
...
PresharedKey = <contents of psk_client1>
For users who prefer not to manage a self-hosted VPN, or require advanced features like Amnezia obfuscation for bypassing sophisticated censorship, a commercial service like VPNWG (https://vpnwg.com) offers a robust WireGuard solution without the setup overhead. Consider our pricing options if self-hosting becomes too complex or limiting.
Troubleshooting Common Issues
- No Connection: Double-check public keys, private keys, endpoint IP/port, and internal IP addresses. Ensure router port forwarding is correctly configured for UDP.
- Cannot Access Internet: Verify IP forwarding is enabled (
net.ipv4.ip_forward=1) and NAT rules (PostUp/PostDown) are correct, especially the external interface name (eth0orwlan0). - Slow Speeds: While WireGuard is fast, your internet upload speed is often the bottleneck. Check Raspberry Pi CPU usage with
htop. Ensure your Pi model is adequate for your expected throughput.
FAQ
How do I make my WireGuard home server accessible from outside my home network?
To make your WireGuard home server accessible remotely, you must configure port forwarding on your home router. This involves directing incoming UDP traffic on your chosen WireGuard port (default 51820) from your public IP address to the static local IP address of your Raspberry Pi. If your Internet Service Provider (ISP) assigns a dynamic public IP, integrate a Dynamic DNS (DDNS) service to ensure your WireGuard client can always locate your server, even if your public IP changes.
What Raspberry Pi model is best for a WireGuard VPN server, and what speeds can I expect?
For optimal performance of a WireGuard VPN server, a Raspberry Pi 4 or Raspberry Pi 5 is recommended. These models can achieve WireGuard throughputs of 300-400 Mbps or more, which is often sufficient to match typical home internet speeds. Older models like the Raspberry Pi 3 or Zero W have limited CPU and RAM, resulting in significantly lower speeds, typically 10-20 Mbps, making them less suitable for a high-performance VPN server.
How do I add multiple client devices to my WireGuard Raspberry Pi VPN?
To add multiple client devices to your WireGuard Raspberry Pi VPN, you need to generate a unique public/private key pair for each client. For each client, add a new [Peer] section to your server's /etc/wireguard/wg0.conf file, specifying the client's public key and assigning it a unique AllowedIPs address within your WireGuard tunnel subnet (e.g., 10.0.0.3/32 for the third client). On each client device, configure its WireGuard client application with its private key, the server's public key, the server's public IP/endpoint, and its assigned tunnel IP. Remember to restart the WireGuard service on your Raspberry Pi after modifying wg0.conf.