A no-log VPN policy means the VPN service explicitly commits to not collecting, storing, or sharing any data that could identify a user or their online activities. This includes traffic logs, connection logs, IP addresses, DNS queries, or timestamps, making it a critical aspect for anyone seeking true online anonymity and privacy. When a VPN claims to have no logs, it asserts that there is no record of what you do online while connected to their service, which is fundamental to a secure VPN no logs environment. Understanding your chosen VPN logging policy is paramount.
What a No-Log VPN Policy Means
At its core, a no-log VPN policy is a pledge from a VPN provider to safeguard user privacy by eliminating data retention. This policy directly addresses the core purpose of using a VPN: to shield your digital footprint from third parties, including internet service providers, governments, and cybercriminals. Without logs, there is no data to hand over, even under legal pressure.
A true no-log VPN does not record connection times, session durations, bandwidth used, IP addresses assigned, or the websites visited. The absence of these records ensures that your online actions cannot be traced back to you. This commitment to a vpn no logs policy is what differentiates privacy-focused services from those that might inadvertently or intentionally compromise user data.
Understanding VPN Logging Policy: What Data is at Risk?
VPNs operate by routing your internet traffic through their servers, encrypting it in the process. While this enhances security, it also places the VPN provider in a privileged position to observe your activities. A weak VPN logging policy can expose sensitive information.
Common types of data that some VPNs might log include:
- Connection Logs: These record when you connect and disconnect from the VPN, the duration of your session, and sometimes the server you used. While not directly revealing activity, they can establish patterns.
- Bandwidth Logs: Tracking the amount of data transferred can indicate usage levels but typically not specific activities.
- IP Address Logs: This is a major privacy concern. Logging your real IP address (and the IP address assigned by the VPN) directly defeats the purpose of anonymity.
- Activity/Traffic Logs: This is the most dangerous type of log, detailing websites visited, files downloaded, or applications used. Any VPN logging this completely negates privacy.
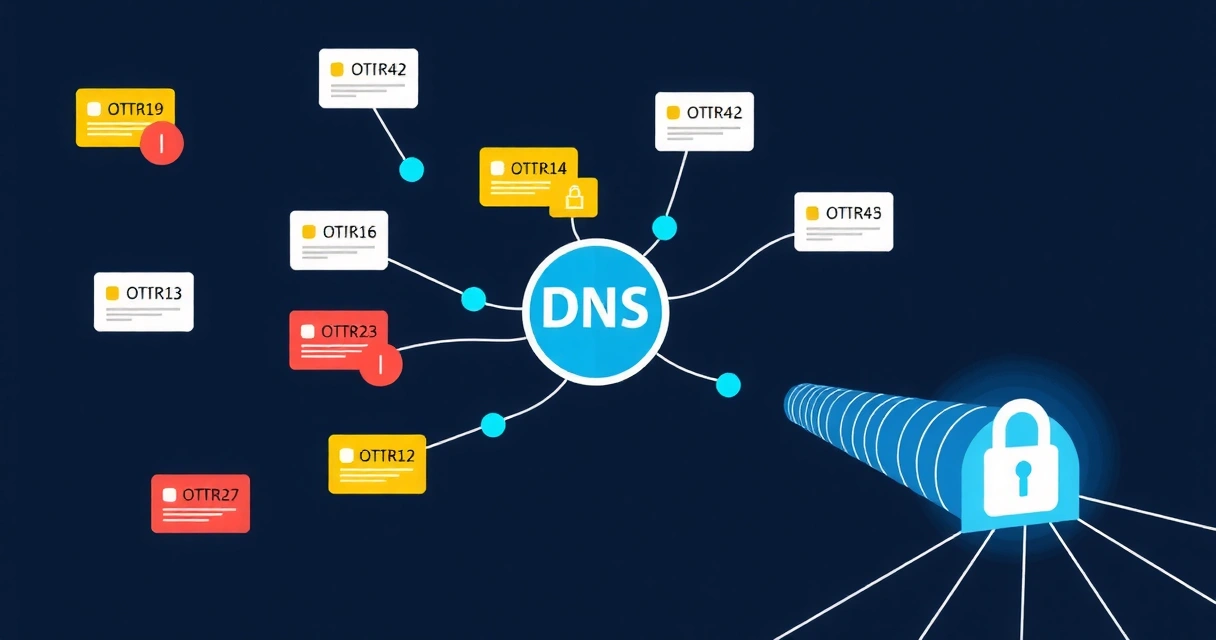
- DNS Query Logs: Recording DNS requests can reveal which websites you attempt to visit, even if the content itself is encrypted. This can be a significant privacy risk, often highlighted when discussing potential DNS leaks.
For example, if a VPN logs your original IP address, and you then visit a site that also logs your (now VPN-assigned) IP address, a government agency could request logs from both the VPN and the website to correlate and identify you. This scenario underscores why a strict no-log vpn policy is non-negotiable for privacy.
Why a Strict VPN No Logs Policy is Essential for Privacy
The primary reason for using a VPN is to enhance privacy and security. A strict VPN no logs policy directly supports this goal by ensuring that your online activities remain private, even from the VPN provider itself. Without logs, there is no metadata or traffic data to compromise your anonymity.
This is crucial in several contexts:
- Data Breach Protection: Even the most secure systems can be breached. If a VPN service is compromised, and it maintains no logs, there is simply no user activity data for attackers to steal.
- Legal Compliance: In jurisdictions where governments can compel companies to hand over user data, a no-log policy means the VPN has nothing to provide. This is especially important for services like GProxy, where anonymity is key.
- Preventing Targeted Advertising: Without logs of your browsing habits, advertisers cannot build detailed profiles of your interests, reducing targeted ads and tracking efforts. This complements the work of services like WebTrackly in understanding web behavior without compromising individual privacy.
Consider the broader landscape of Internet Privacy in 2026; a no-log policy is a fundamental defense against the increasing sophistication of surveillance and data collection. It's not just about hiding; it's about reclaiming control over your digital identity.
Methods to Verify a VPN's No-Log Claims
Verifying a VPN's no-log claims requires a multi-faceted approach, as simply trusting a provider's marketing can be risky. Due diligence is essential to ensure your chosen VPN truly adheres to a no log vpn policy.
Independent Audits
The most credible way to verify a no-log claim is through independent security audits conducted by reputable third-party firms. These audits involve experts reviewing the VPN's infrastructure, code, servers, and internal policies to confirm that no user data is being logged or stored. Look for detailed audit reports that are publicly available, not just summary statements. Services like Secably can perform similar assessments for other infrastructure, highlighting the importance of external validation.
Jurisdiction and Legal Framework
The country where a VPN company is legally incorporated plays a significant role. Some countries have mandatory data retention laws that could force a VPN to log user data, regardless of their stated policy. Opt for VPNs based in privacy-friendly jurisdictions without such laws. For instance, VPNWG operates with a strict no-logs policy, leveraging the legal environment of its operational base to uphold user privacy.
Transparency Reports
Some VPN providers publish transparency reports detailing any requests for user data they have received and, critically, how they responded (e.g., that they had no data to provide). While not a direct audit, these reports demonstrate a commitment to openness and accountability regarding their VPN logging policy.
Real-World Cases
Examine whether the VPN provider has ever been subpoenaed or involved in a legal case where user data was requested. If the provider was unable to provide data because they genuinely had none, it serves as strong evidence of their no-log commitment. Conversely, if they have handed over logs, their claims are demonstrably false.
Technology and Configuration
The technical implementation also matters. A VPN that uses RAM-only servers (diskless servers) cannot permanently store data, as all data is wiped on reboot. This architectural choice inherently supports a no-log policy. WireGuard, known for its lean codebase and cryptographic design, is an excellent protocol choice for privacy-focused services like VPNWG, which pairs it with Amnezia obfuscation to further enhance security. For those interested in the underlying tech, learning how to Build a WireGuard VPN Server can offer insights into these configurations.
Technical Measures for a Truly No-Log VPN
Beyond policy statements, a truly no-log VPN implements specific technical safeguards. These measures are designed to prevent data logging at an architectural level.
RAM-Only Servers
As mentioned, utilizing RAM-only servers (also known as volatile memory servers) is a robust technical defense against logging. With no persistent storage, any operational data exists only in temporary memory and is erased immediately upon server reboot or power cycle. This makes it impossible for logs to be seized or recovered, even if physical access to the server is gained.
Strong Encryption and Secure Protocols
While not directly related to logging, strong encryption (e.g., AES-256) and modern, secure VPN protocols like WireGuard ensure that even if traffic metadata were somehow observed, its content remains unreadable. VPNWG, for example, combines WireGuard's efficiency with Amnezia obfuscation, providing an additional layer of privacy against deep packet inspection.
Kill Switch Implementation
An essential feature for any privacy-focused VPN is a VPN kill switch. This mechanism automatically blocks all internet traffic if the VPN connection drops, preventing your real IP address or unencrypted data from being exposed, even for a moment. This prevents accidental logging by your ISP or other third parties.
Self-Owned and Managed Infrastructure
VPN providers who own and manage their entire server network have greater control over their infrastructure's security and logging policies. Leasing servers from third parties introduces an additional layer of trust and potential vulnerability. Services that control their own hardware can ensure strict configurations are applied consistently.
Choosing a No-Log VPN: Considerations
When selecting a VPN, prioritize those that demonstrate a clear, verifiable commitment to a no-log policy. Look for the technical details and evidence discussed above. A transparent VPN provider will openly share information about their infrastructure, audits, and legal jurisdiction.
Consider VPNWG (https://vpnwg.com) as an example. It's a WireGuard + Amnezia obfuscation VPN service built with a strong focus on privacy, aiming to provide a secure, no-log experience. Our pricing structure reflects a commitment to delivering premium privacy features without compromising on performance. Services that are upfront about their technology and operational choices often provide greater confidence in their privacy claims, including those focused on Mobile VPN Security.
Summary Table: Logged vs. No-Log VPNs
| Feature | Logged VPN | No-Log VPN |
|---|---|---|
| IP Address Storage | Often stores real IP and assigned IP. | Never stores real IP or assigned IP. |
| Connection Timestamps | Records connection start/end times. | No record of connection times. |
| Bandwidth Used | May track data transfer. | Does not track bandwidth per user. |
| Activity/Traffic Data | May log websites visited, downloads. | No record of online activities. |
| DNS Queries | May log DNS requests. | No record of DNS queries. |
| Server Type | Typically uses standard servers with persistent storage. | Often uses RAM-only (diskless) servers. |
| Audits/Verification | Rarely audited, or audits are not public. | Regularly undergoes independent, public security audits. |
| Jurisdiction Risk | Higher risk if based in data retention countries. | Lower risk in privacy-friendly jurisdictions. |
FAQ
What is the difference between a no-log VPN and a zero-log VPN?
The terms "no-log VPN" and "zero-log VPN" are generally used interchangeably to describe a service that does not record any user identifiable data or online activities. There is no official technical distinction between them; both terms signify a commitment to the highest level of privacy by not retaining connection, traffic, or personal data logs. What matters is the verifiable implementation behind the claim, often confirmed through independent audits.
Can a VPN truly guarantee 100% no logs?
While no technology can offer a 100% absolute guarantee against all theoretical threats, a well-implemented no-log VPN policy, backed by independent audits, RAM-only servers, and a privacy-friendly jurisdiction, comes as close as practically possible. These technical and operational measures significantly reduce the risk of any user data being compromised or identified, offering robust privacy protection.
Why do some VPNs claim no logs but still collect some data?
Some VPNs might claim "no logs" but still collect anonymized connection data or basic usage statistics to maintain service quality or troubleshoot issues. This data is usually non-identifiable and cannot be linked back to individual users. However, a truly strict no-log policy means even this aggregated data is minimized or not collected at all. It's important to read the privacy policy carefully to understand what, if any, non-identifying data is collected.