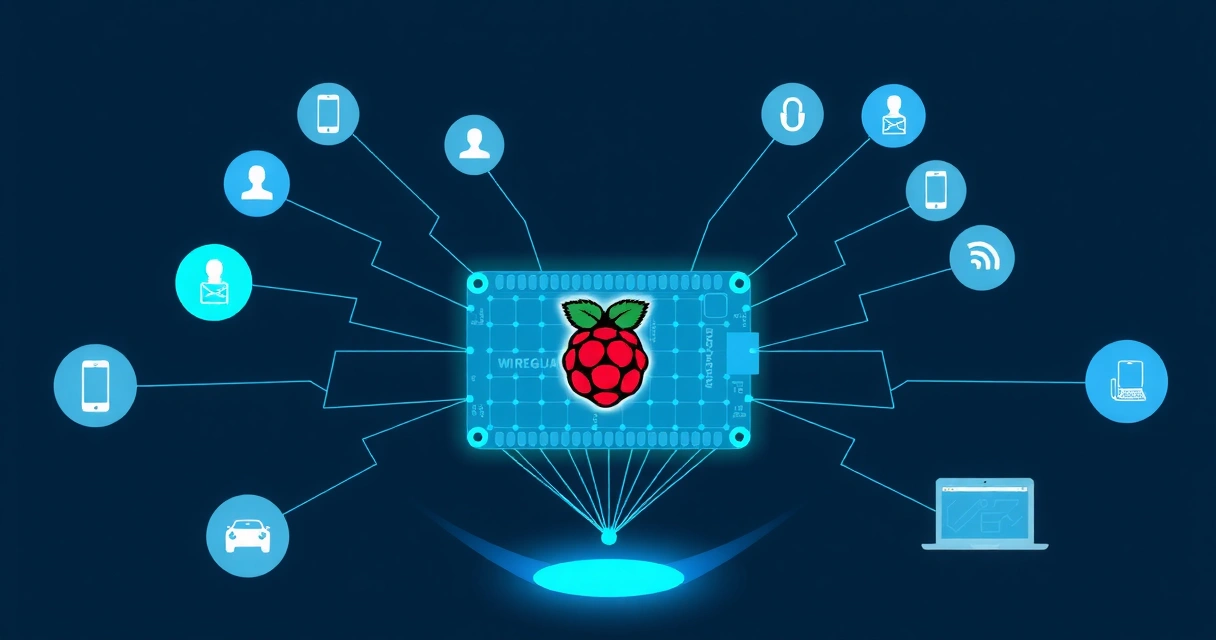
Setting up a WireGuard VPN server from scratch involves preparing a Linux server, generating secure cryptographic keys for both the server and its clients, configuring network interfaces, and enabling IP forwarding. This process ensures a private and secure connection for your devices, routing traffic through your self-hosted server.
Preparing Your Linux Server
Before installing WireGuard, ensure your Linux server is updated and has the necessary kernel modules. Most modern Linux distributions, like Ubuntu or Debian, include WireGuard kernel modules by default. Begin by updating your package lists and upgrading existing packages.
sudo apt update && sudo apt upgrade -yNext, install the WireGuard tools. These tools provide the wg and wg-quick commands used for configuration and management.
sudo apt install wireguard -yEnable IP forwarding on your server. This is crucial for the VPN to route traffic from clients to the internet. Edit /etc/sysctl.conf and uncomment or add the line net.ipv4.ip_forward=1.
sudo nano /etc/sysctl.confAfter saving the file, apply the changes without rebooting:
sudo sysctl -pConfigure your server's firewall to allow incoming UDP traffic on the WireGuard port, typically 51820. Using UFW (Uncomplicated Firewall) as an example:
sudo ufw allow 51820/udp
sudo ufw enable
sudo ufw statusAlways verify your firewall rules. Before exposing your server to the internet, consider using tools like Zondex to scan for unintentionally exposed services or open ports beyond what is intended for your VPN.
Generating WireGuard Keys and Configuration
WireGuard uses public-key cryptography for secure communication. You need to generate a private and public key pair for both the server and each client.
First, create a directory for WireGuard configurations and set strict permissions:
sudo mkdir -p /etc/wireguard
sudo chmod 700 /etc/wireguard
cd /etc/wireguardGenerate the server's private and public keys:
sudo wg genkey | sudo tee privatekey_server | sudo wg pubkey | sudo tee publickey_serverRepeat this process for each client you plan to connect. For example, for 'client1':
sudo wg genkey | sudo tee privatekey_client1 | sudo wg pubkey | sudo tee publickey_client1Store these keys securely. The private key must remain secret, while the public key can be shared with peers.
Configuring the WireGuard Server
Create the WireGuard server configuration file, typically named wg0.conf, in the /etc/wireguard/ directory. This file defines the server's interface, its private key, listening port, and how to handle client connections.
sudo nano /etc/wireguard/wg0.confPopulate the file with the following structure, replacing placeholders with your actual keys and network interface name (e.g., eth0, ens3). You can find your public interface name using ip a.
[Interface]
PrivateKey = <server_private_key>
Address = 10.0.0.1/24
ListenPort = 51820
PostUp = iptables -A FORWARD -i %i -j ACCEPT; iptables -A FORWARD -o %i -j ACCEPT; iptables -t nat -A POSTROUTING -o <your_public_interface> -j MASQUERADE
PostDown = iptables -D FORWARD -i %i -j ACCEPT; iptables -D FORWARD -o %i -j ACCEPT; iptables -t nat -D POSTROUTING -o <your_public_interface> -j MASQUERADE
[Peer]
# Client 1
PublicKey = <client1_public_key>
AllowedIPs = 10.0.0.2/32
PersistentKeepalive = 25The Address defines the server's IP within the VPN tunnel. PostUp and PostDown commands enable NAT (Network Address Translation) for clients to access the internet through the server. The [Peer] section lists each client, using their public key and assigning them an internal VPN IP address.
Client Configuration and Connection
Each client needs its own configuration file. Create a file for 'client1' (e.g., client1.conf) on the client device. This file will define the client's private key, its VPN IP address, and details about the server peer.
[Interface]
PrivateKey = <client1_private_key>
Address = 10.0.0.2/32
DNS = 8.8.8.8, 1.1.1.1 # Or your preferred DNS servers
[Peer]
PublicKey = <server_public_key>
Endpoint = <server_public_ip>:51820
AllowedIPs = 0.0.0.0/0 # Route all traffic through the VPN
PersistentKeepalive = 25Transfer this client1.conf file to the client device. On a Linux client, you can place it in /etc/wireguard/. For Windows, macOS, or mobile clients, the WireGuard application allows importing configuration files or QR codes.
Once the configuration files are in place, enable and start the WireGuard service on the server:
sudo systemctl enable wg-quick@wg0
sudo systemctl start wg-quick@wg0
sudo wg showOn the client, activate the VPN connection. For Linux, assuming the config is /etc/wireguard/client1.conf:
sudo wg-quick up client1
sudo wg showAfter connecting, verify your public IP address to confirm traffic is routing through your VPN server. Services like WebTrackly can help monitor web traffic and ensure privacy for your users, though for a personal VPN, a simple IP check is sufficient.
Troubleshooting and Best Practices
If you encounter issues, start by checking logs on both the server and client:
sudo journalctl -u wg-quick@wg0Common problems include incorrect public/private keys, firewall rules blocking traffic, incorrect IP forwarding settings, or an unreachable server endpoint. Ensure your server's public IP address is correct in the client configuration.
Always use strong, unique keys for each peer. Regularly update your server's operating system and WireGuard software to patch security vulnerabilities. While setting up a WireGuard VPN from scratch provides maximum control, it requires technical expertise. For users seeking a managed, high-performance WireGuard solution without the setup complexity, services like VPNWG offer pre-configured servers and dedicated support, often incorporating advanced features like DPI bypass for regions with strict internet censorship, similar to a VPN for China or VPN for Russia.
FAQ
Why choose WireGuard over other VPN protocols like OpenVPN?
WireGuard is significantly simpler, faster, and more efficient than older protocols like OpenVPN. It uses modern cryptographic primitives, resulting in a smaller codebase that is easier to audit and maintain. This leads to better performance, lower latency, and improved battery life on mobile devices compared to OpenVPN.
How do I add more clients to my WireGuard server?
To add more clients, generate a new private and public key pair for each new client. Then, append a new [Peer] section to your server's /etc/wireguard/wg0.conf file. Assign a unique AllowedIPs address (e.g., 10.0.0.3/32 for the third client). After updating the server config, restart the WireGuard service using sudo systemctl restart wg-quick@wg0. Finally, create a corresponding client configuration file for the new peer.
My WireGuard connection drops frequently. What should I check?
Frequent drops can be due to several factors. First, ensure the Endpoint IP address in your client configuration is correct and the server is publicly reachable. Check server firewall rules (e.g., UFW) to ensure UDP port 51820 is open. On the client, adding PersistentKeepalive = 25 to the [Peer] section can help maintain connections through NAT devices or firewalls by sending a small UDP packet every 25 seconds. Also, verify that IP forwarding is enabled on the server.
Further Reading
For more on related topics, check out our articles on VPN Kill Switches: Essential for Data Protection and Privacy and Mobile VPN Security: Protecting Your Phone Connections.